An advanced connector for extending Guardium for Adabas AdaGuard was developed to extend the ability of IBM’s Infosphere Guardium product to monitor SAG’s ADABAS database update activity. The cost to monitor updates is reduced by feeding the ADABAS PLOG (protection log) data into Guardium
AdaGuard

How does it work?
As each PLOG becomes available AdaGuard extracts and reformats the data manipulation commands for processing by Guardium. It is not necessary to convert every single command as only the commands that touched data items that are deemed to be sensitive can be selected. Benefits Monitoring of ADABAS update activity is possible at a reasonable cost. This easy to implement solution allows the end user to monitor updates to the Adabas data base along with the RDBMS’s supported by Guardium. ADABAS users are able to store the audit data off the actual server monitored enabling:- Audit and log information cannot be erased to cover nefarious breaches to the Guardium device.
- Separation of duties can be maintained to ensure correct audit information is captured.
- Privileged users cannot tamper or alter audit logs as they do have access to these files.
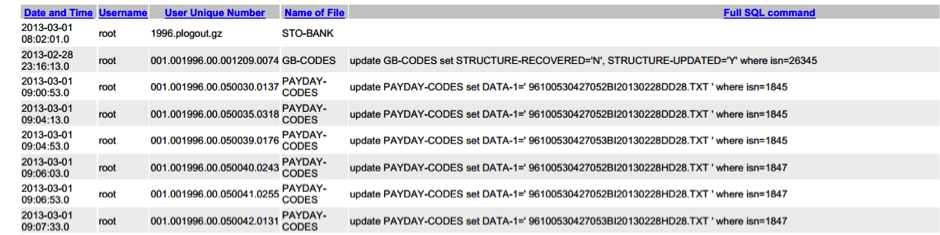
AdaGuard monitors all root and privileged user activity performed on the ADABAS database infrastructure as illustrated in the following sample report: